Not all EDR platforms are built the same, and the gap between CrowdStrike EDR and traditional endpoint detection tools has widened considerably as attack techniques have grown more sophisticated. Understanding what that gap actually consists of — beyond marketing language — is the starting point for any organization evaluating endpoint security options in 2026.
According to Mordor Intelligence, the global EDR market is projected to grow from USD 5.11 billion in 2025 to USD 18.68 billion by 2031 at a CAGR of 24.16%, with CrowdStrike among the top five vendors capturing roughly 58% of the total 2025 EDR revenue. That dominance reflects something real — not just brand recognition, but a platform that consistently outperforms legacy approaches across detection accuracy, operational overhead, and response speed.
What “Traditional EDR” Actually Means
Traditional EDR refers to platforms built on signature-based or rule-based detection architectures, typically deployed through on-premise infrastructure or hybrid models that rely heavily on local processing. These tools were a significant step forward from antivirus in their time — they introduced continuous monitoring, endpoint telemetry, and basic behavioral alerts that signatures alone couldn’t provide.
The limitations, however, are structural:
- Signature-based detection requires the threat to be known before it can be identified — zero-days and novel malware variants are invisible to hash-matching engines
- Rule-based correlation catches deviations from defined patterns, but attackers who understand those rules can operate within them indefinitely
- Living-off-the-land techniques that abuse legitimate system tools produce no suspicious files to scan, bypassing traditional detection entirely
- On-premise architectures face a constant tension between telemetry depth and endpoint performance, often forcing organizations to reduce data collection to avoid agent overhead
For a direct look at how this plays out in practice, ClearNetwork’s comparison of EDR vs antivirus solutions covers the capability evolution from traditional protection to modern endpoint defense in concrete terms.
CrowdStrike EDR: Architecture as the Foundation
The distinction that matters most about Falcon isn’t any single feature — it’s the cloud-native architecture underpinning the entire platform. CrowdStrike’s Falcon platform processes telemetry in the cloud rather than on the endpoint, which resolves the performance-versus-visibility tradeoff that constrains traditional deployments.
The Falcon agent requires minimal system resources — ClearNetwork’s deployed instances confirm approximately 20MB disk, 25MB RAM, and a maximum 3% CPU — while the intelligence layer operates at full capacity in the cloud.
That cloud layer ingests events from across CrowdStrike’s entire customer base — billions of endpoint events processed daily — and feeds them into AI and machine learning models that improve continuously with scale. An attack pattern encountered in one organization is recognized across all others within minutes. Traditional EDR platforms operating in isolation cannot replicate this collective intelligence effect.
Behavioral Detection Without Signatures
Falcon identifies threats by analyzing what processes are doing, not what files look like. Rather than matching against a known-bad signature, Falcon evaluates process behavior, parent-child relationships, network connections initiated by processes, and execution context — then scores activity against models trained on adversary behavior across CrowdStrike’s threat intelligence network.
This matters most for the attack categories traditional tools consistently miss:
- Fileless malware that executes entirely in memory and never writes to disk
- Credential theft carried out through legitimate system tools like PowerShell or WMIC
- Staged attacks that distribute malicious activity across multiple processes to stay under individual detection thresholds
- Living-off-the-land techniques that blend into normal administrative behavior until lateral movement begins
Threat Intelligence Integration
Traditional EDR platforms typically rely on commercial threat feeds that update on a scheduled basis. CrowdStrike’s threat intelligence is generated internally by its Adversary Intelligence team, which actively tracks and profiles specific threat actor groups — their tools, infrastructure, targeting patterns, and behavioral signatures. This intelligence feeds directly into Falcon’s detection models rather than being applied as a separate lookup layer.
The operational implication is significant. When Falcon detects activity associated with a known threat actor group, analysts receive context — not just an alert, but information about who is likely behind it, what their typical objectives are, and what lateral movement or persistence mechanisms to expect next. That context changes how incidents are prioritized and how the response unfolds.\
CrowdStrike EDR Features and Capabilities: Key Differentiators
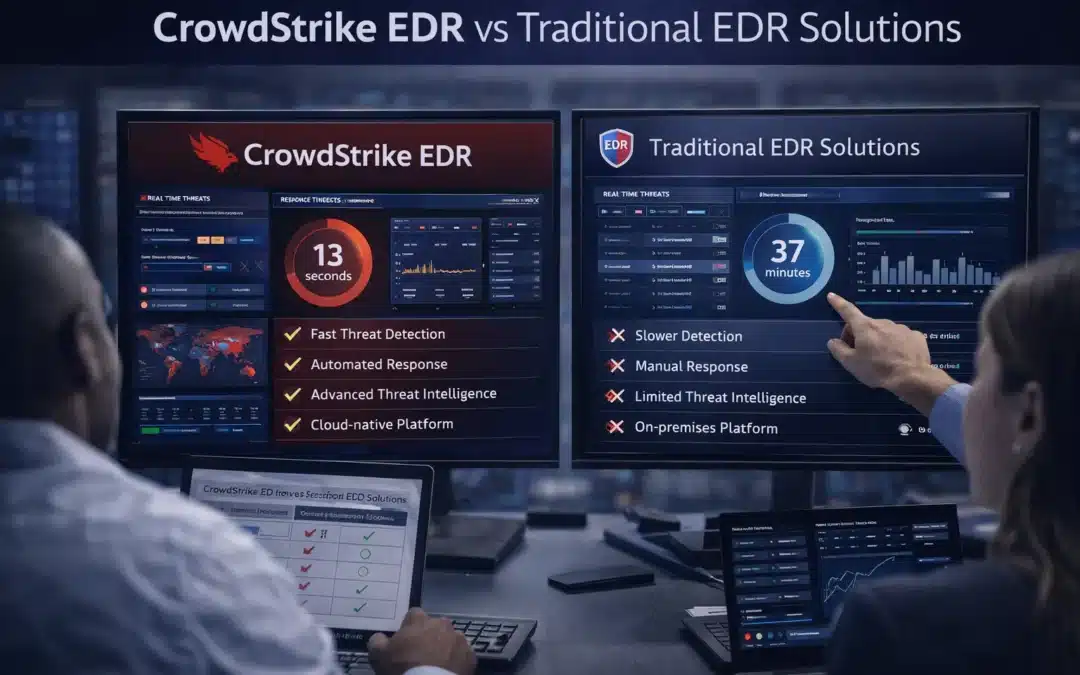
| Capability | CrowdStrike Falcon | Traditional EDR |
| Detection approach | Behavioral AI + threat intelligence | Signature-based + rule-based |
| Telemetry processing | Cloud-native, minimal agent overhead | On-premise or hybrid, higher resource usage |
| Zero-day coverage | Strong — no signature required | Weak — unknown threats evade detection |
| Threat intelligence | Internal Adversary Intelligence team, real-time | Commercial feeds, scheduled updates |
| Investigation tooling | Process tree visualization, remote access | Manual log correlation |
| Automated response | Configurable autonomous containment | Alert-only or limited automation |
| Collective intelligence | Cross-customer threat data shared in real time | Isolated per-deployment |
Real-Time Visibility and Investigation Depth
CrowdStrike EDR features and capabilities include a process tree visualization that maps every event on an endpoint — parent processes, child processes, network connections, file writes, registry modifications — into a coherent timeline.
Analysts investigating an incident see the full attack chain without having to reconstruct it from raw log data. This reduces investigation time substantially compared to traditional platforms, where forensic reconstruction is largely manual.
The Falcon interface also supports real-time remote access to any endpoint in the environment, allowing analysts to execute queries, collect additional evidence, or initiate response actions without disrupting the end user or requiring physical access.
Automated Response and Containment
The platform’s automated response actions execute based on detection confidence thresholds — isolating compromised endpoints from the network, terminating malicious processes, and blocking execution of identified threat indicators. These actions can be configured to run autonomously for high-confidence detections or to require analyst confirmation for lower-confidence events.
Traditional EDR platforms typically offer more limited automated response, often defaulting to alerting and requiring manual analyst action for containment. In environments without dedicated security staff available around the clock, that gap translates directly into longer dwell times. Understanding how managed EDR closes this operational gap is covered in depth in ClearNetwork’s overview of what managed EDR security involves.
Where Traditional EDR Still Has a Role
Traditional EDR platforms aren’t without merit in specific contexts. Scenarios where on-premise or legacy tools remain the practical choice include:
- Strict data sovereignty requirements that prohibit sending endpoint telemetry to external cloud infrastructure
- Air-gapped or near-air-gapped networks in critical infrastructure where cloud connectivity isn’t available or permitted
- Legacy hardware environments running older operating systems that modern agents don’t support
- Low-resource endpoints where Falcon’s cloud processing model introduces connectivity dependencies that the device can’t sustain
That said, for the majority of organizations operating standard IT environments, the performance advantage of modern cloud-native EDR outweighs on-premise flexibility by a substantial margin. For a broader view of how EDR compares to managed detection and response approaches, ClearNetwork’s MDR vs EDR comparison explains where the two models diverge and which scenarios favor each.
The Managed CrowdStrike Advantage
Running a CrowdStrike EDR solution effectively requires more than deploying the agent. Falcon generates rich, actionable telemetry — but only if the alerts it surfaces are reviewed, triaged, and acted on promptly. Organizations without dedicated security analysts available at all hours get the detection capability without the response capacity to use it.
The result is enterprise-grade endpoint security without the staffing requirements of building an internal SOC around the platform. For organizations that have concluded CrowdStrike is the right technology but lack the internal resources to operate it fully, the managed model closes that gap. Contact ClearNetwork to discuss which deployment approach fits your environment.