News & Resources
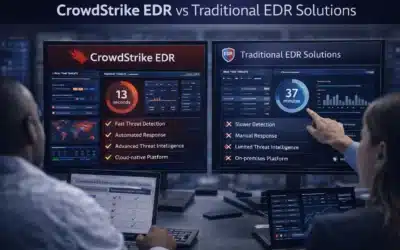
CrowdStrike EDR vs Traditional EDR Solutions: A Comprehensive Comparison
Not all EDR platforms are built the same, and the gap between CrowdStrike EDR and traditional endpoint detection tools has widened considerably as attack techniques have grown more sophisticated. Understanding what that gap actually consists of — beyond marketing...
What to Expect from Leading EDR Solution Providers in 2026
The expectations organizations bring to EDR solution providers have shifted considerably. A few years ago, behavioral detection and automated response were differentiators. In 2026, they are the baseline. What separates strong providers from the rest has moved up the...
SIEM Solutions Comparison: Key Features and Benefits of Leading Platforms
Any meaningful SIEM solutions comparison has to go beyond spec sheets. Feature parity across major platforms has grown significantly — most enterprise-grade tools now check the same foundational boxes. What actually separates them is detection architecture, pricing...
Exploring SIEM Options for Top Security Operations: Which One Is Right for You?
Finding the right SIEM options for top security operations has never involved more variables. Cloud-native architecture, OT network convergence, AI-driven detection, and the widening cybersecurity skills gap have all reshaped what "the right SIEM" actually means in...
Comparing the Top SIEM Platforms: Features, Benefits, and Pricing
Choosing a SIEM platform has never been more complicated — or more consequential. The market has consolidated significantly, AI capabilities have moved from novelty to core expectation, and cloud-native deployment has shifted from a preference to a near-requirement...
The Future of Network Security Monitoring: Trends and Innovations for 2026
The way organizations monitor their networks has changed more in the past three years than in the previous decade. Hybrid infrastructure, cloud-native workloads, remote endpoints, and a threat landscape that weaponizes AI have collectively forced a fundamental...
The Role of Cyber Threat Intelligence Services in Real-Time Threat Detection
Security teams don't lose to attackers because they lack tools. They lose because they're reacting to threats that intelligence could have anticipated hours — or days — earlier. Cyber threat intelligence services change that equation by giving defenders the context...
Top SOC as a Service Providers for 2026: What You Need to Know
Running a Security Operations Center in-house has always been expensive. Staffing it around the clock, with analysts skilled enough to catch sophisticated threats, is even harder. That's exactly why the market for top SOC as a service providers has expanded so rapidly...
Top 5 Best EDR Products for Endpoint Protection in 2026
Endpoint security is no longer optional—it's the front line of every serious cybersecurity posture. As attacks grow more targeted and automated, the gap between organizations running a capable EDR product and those relying on legacy antivirus has never been wider....
How Best SIEM Solutions for Enterprises in 2026 Help Automate Security Operations
The role of a Security Information and Event Management (SIEM) system has shifted from being a passive library of logs to becoming the central brain of the modern enterprise. As we move through 2026, the sheer volume of data generated by cloud workloads, remote...
Top 10 Features to Look for in the Best MDR Software for Small Business Security
Small businesses are not the afterthought cybercriminals skip over—they're a primary target. The best MDR software for small business security has to do more than monitor logs. It needs to detect, investigate, and respond before a threat becomes a crisis, all without...
Building a Resilient IT Infrastructure Security Strategy for Your Organization
In an era where digital operations are the lifeblood of every enterprise, the concept of a perimeter has fundamentally changed. We are no longer defending a single fortress; we are securing a sprawling, interconnected ecosystem that lives in the cloud, on employee...